File this one under ‘oh, crap’, because if you’re a Grindr, Jack’d or Hornet (or indeed, all of them) user then you should know that the apps have the potential to leak your location data.
Three computer security researchers at Kyoto University, Japan have released a paper detailing how users of those apps can have their location pinpointed to a scary degree and with relative ease.
You think you’re safe because you’ve switched off location within the app? Wrong!
That might be embarrassing at the least, or potentially something far, far worse for users in the 76 countries in which it’s still illegal to be homosexual.
Essentially, the problem is one that’s going to be hard to avoid in the long-term. All of the apps use location to show other users nearby – it’s sort of the whole point.
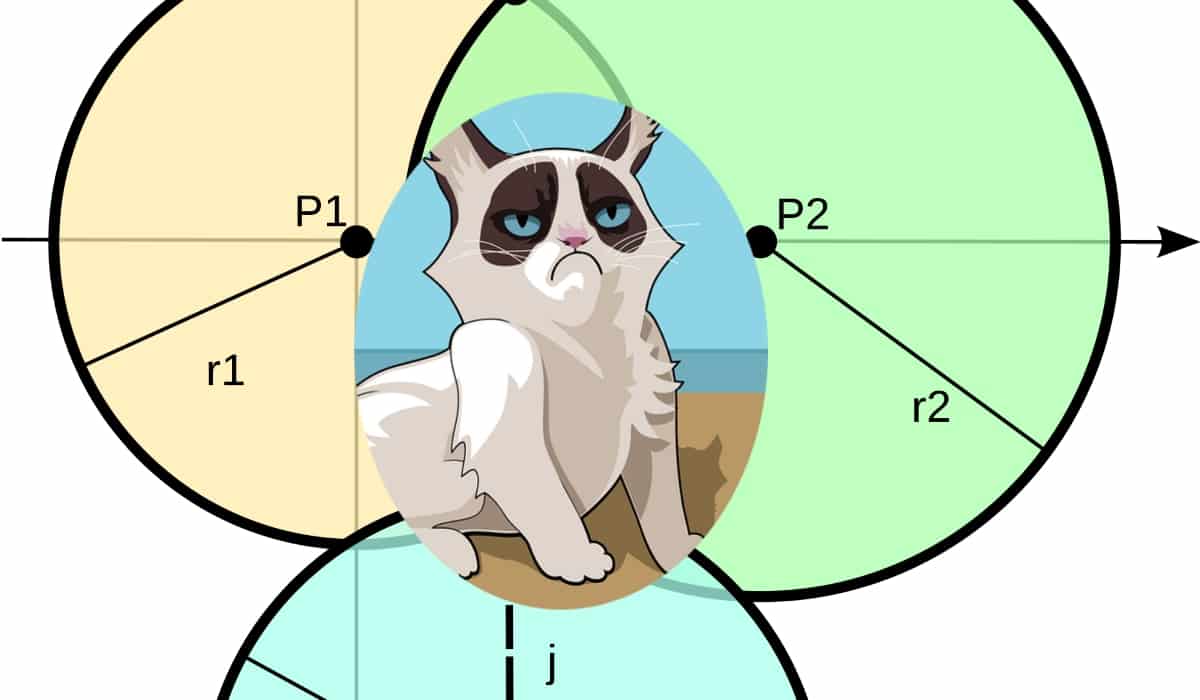
However, the researchers say that by using trilateration (identifying location by measuring from three overlapping points), you can pinpoint a specific person.
All three apps offer privacy and security features, and partially rebutted claims made in the paper in a statement to Wired but the researchers insist that even after the apps had been updated, they were still identify location data.
If all that sounds pretty unlikely consider this: all you need is an Android device and an app that spoofs GPS location (plus some dummy accounts) to do it yourself.
And if you intend to carry on using them anyway, you may as well go ahead and download a GPS spoofing app (you’ll need a jailbroken iPhone if you’re an Apple user) so that you can protect against your own real location.
We’ve contacted all three companies and will update if they respond.
> Your Neighbors Are My Spies: Location and other Privacy Concerns in GLBT-focused Location-based Dating Applications (PDF via Wired)